In this Article:
- What are your biggest cyber security risks?
- How does cyber security awareness training work?
- What is the importance of cyber security awareness?
- What are some of the most common social engineering scams?
- Which departments are the most vulnerable to phishing scams?
- What are some essential cyber security awareness tips?
- Who are some of the top cyber security awareness training vendors?
- What else do I need to protect my business against security threats?
Cyber security awareness training is a relatively new but rapidly expanding service industry built around combating phishing and other malicious social engineering tactics used by hackers. Social engineering is the use of psychological manipulation to obtain the trust of an unwitting end-user. Meanwhile, targeted attacks to businesses, especially small to medium-sized organizations, have become more prevalent. Therefore, these security awareness training programs attempt to train human error out of the equation.
For this post, we picked the brains of the senior technicians and management at Capital Network Solutions to offer some security awareness training answers and advice. Every business is a little bit different, and one size does not fit all. However, we based the best practices outlined in this article on our 30 years of experience providing managed IT services and network security solutions to businesses throughout the Sacramento area.
What are your most significant cyber security risks?
We all know the terrifying true-life tales of mass data breaches and other heinous cyber security crimes. Foreign and domestic threat actors evolve their schemes every day, developing ever more sophisticated methods and state-of-the-art technologies to penetrate past your security protocols. Hackers are attacking everything from school systems to international corporations, looking for private information to hold for ransom or sell on the “dark web.”
However, the greatest cyber security threat in the modern world comes not from outside your organization, but rather from inside.
According to recent studies, the most prominent cyber security risk to American businesses is employee negligence. In other words, simple human error. Phishing, or the process of creating fraudulent emails to obtain confidential information, targets untrained and unsuspecting end users. Meanwhile, the more personalized attacks known as spear phishing have become increasingly prevalent. Even with spam filters and other security measures in place, about 15% of phishing emails still reach your employee inboxes.
THE WEAKEST LINKS
Inattentive, poorly trained employees unfamiliar with basic IT practices can unknowingly create security vulnerabilities in your network. Hackers are trying to steal passwords and banking account information, install malware and initiate fraudulent wire transfers. Your employees may be the last line of defense against a phishing attack. However, without proper security awareness training, they could also be the weakest link that allows the bad guys in the door.
- 92% of organizations reported that their biggest security concern is their employees.
- 47% of business leaders claimed that human error caused a data breach at their organization.
- According to Microsoft research, 43% of cyberattacks target small and medium-sized businesses.
- Security software firm Trend Micro found that 91% of cyberattacks and the resulting data breach started with a spear-phishing email.
- A study by Okta found that 49% of employees never participated in security training at work.
- Data breaches cost companies an average of $3.6 million globally in 2017. However, lost money from phishing attacks gets recovered only 4% of the time.
Despite these scary statistics, many organizations lack the budget and training to guard against these threats. Half of all workers admit to clicking on unknown links from suspicious senders, but as a business leader, you have no idea which half. That’s why there is a fast-growing industry that offers security awareness training programs, with the intent of turning vulnerable end-users into human firewalls.
How does cyber security awareness training work?
There are many different vendors offering security awareness training programs, but they all work in mostly the same way.
ASSESSMENT
Security awareness training begins with a baseline test to measure the “phish-prone” percentage of your organization and your employees. KnowBe4, one of the top security awareness training vendors on the market, estimates an “Initial Baseline Phish-prone Percentage” of 27% for their clients. In other words, without proper training, 27% of employees across all industries will likely fall for a phishing scam.
TRAINING
Interactive training modules educate employees about various forms of social engineering scams and how to recognize suspicious emails. Meanwhile, employees learn why they should not click on potentially malicious links from unknown senders. End-users get taught that every email is a potential phishing attack.
SIMULATED PHISHING ATTACKS
Persistent vulnerabilities get exposed through “simulated social engineering testing.” That means that security awareness software randomly sends fake phishing emails to employees. The employees either successfully report the attack, or they click a malicious link. In the latter case, a potential catastrophe turns into a teaching moment. Meanwhile, you gain access to spam email templates and a myriad of customization options. These options allow you to mimic the types of phishing lures likely to be dangled before your employees.
REAL-TIME STATISTICAL REPORTING
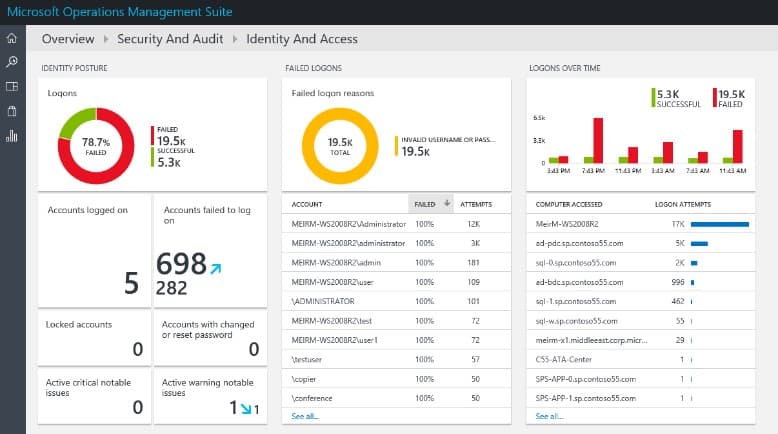
Executives receive real-time statistical data showing which workers in which departments are clicking on these fake phishing scam emails and how often.
FOLLOW-UP AND REMEDIATION
With security awareness programs, training is not just a passive, one-time event without any followthrough. The critical thing to remember is that end-users are not IT experts. However, by teaching security issues through real-world situations and providing instant feedback, complex concepts become relatable and easier to understand.
What is the importance of cyber security awareness?

According to FBI statistics, business email compromise (BEC) and email account compromise (EAC) scams have cost businesses over $12.5 billion worldwide since October 2013. Meanwhile, BEC/EAC scams have been reported in all 50 states and 150 countries across the globe. It seems like the problem is only getting worse. Identified global losses increased 136% in the period between December 2016 and May 2018.
French film production company and cinema chain Pathé fell victim to a costly phishing scam in 2017. Pathé lost $21 million after the two-person senior management team for its Amsterdam-based subsidiary fell victim to a BEC attack. Hackers spoofed the email of Pathé CEO Marc Lacan and sent a message to senior management asking for money to be wired to an account in Dubai. It took three weeks after the initial attack for Pathé to spot the fraud. However, the finance director and managing director were both suspended and ultimately fired.
What are some of the most common social engineering scams?
An alarming 98% of cyberattacks rely on social engineering, a practice that uses psychological manipulation to obtain the trust of an unwitting user. The Pathé story offers a recent, high-profile example of CEO fraud, one of the most common social engineering scams out there.
Here are some of the other social engineering methods widely used by modern hackers:
Phishing
Attempting to steal passwords or other credentials by sending fake emails that pretend to be from reputable sources. According to the most recent Microsoft Security Intelligence Report, inbound emails that were phishing messages increased 250% between January and December 2018. Phishing takes many forms, including the more personally targeted attacks known as spear phishing, as well as domain spoofing, user impersonation and text lures.
Ransomware
Malicious software that seizes or lock up your data, which is then ransomed back to you by the hacker. Enterprise Strategy Group research found that 63% of organizations experienced an attempted ransomware attack in 2017, while 22% said that it happened every week. While attacks declined sharply in 2018, ransomware threatens your internal machines as well as your cloud data.
Malware
Another type of malicious software, this time designed to gain access to and harm your system. Instead of attempting to expose a technical flaw in the system, 97% of malware attacks use some type of social engineering scheme.
Brute-force attacks
Trial-and-error password-guessing sessions performed rapidly by a specialized program that uses your personal information.
Spidering
The practice of gathering information from company websites or social media sites such as Facebook and LinkedIn to come up with word lists. Those credentials then get used to levy brute-force attacks.
What departments are the most vulnerable to phishing scams?
Everyone with an email account and online access is a potential target. However, hackers tend to go after people with the most access to funds and sensitive information like passwords and social security numbers. Therefore, these four departments most often get targeted by hackers:
-
Finance department
-
Executive management (e.g., CEOs or CFOs)
-
IT department
-
Human Resources department
Ultimately, every department in every industry is vulnerable to attack, which only underlines the importance of getting your entire company involved with the task of information security.
What are some remedial cyber security awareness tips?
Improve password security – A study by Okta found that 40% of respondents use and reuse the same two to four passwords. Meanwhile, 10% of respondents admitted they only use one password for everything. Therefore, you should insist on more password complexity from your employees. You should also consider instituting Multifactor Authentication, which blocks attackers from gaining access to your network and brute-forcing into cloud-based email accounts.
Think before you click – There are a few ways to identify a spam email quickly:
- Look at the Sent address. Much of the time, the domain will be one or two letters, numbers or symbols different from the correct address.
- Make sure the email is in HTML format. If you receive an email in plaintext or rich text format, that’s something to raise an eyebrow over.
- Be suspicious of attachments. If you’re not expecting a shipment from Amazon, don’t click a suspicious delivery link. Stop, think and process the available information before you click.
Take the time to talk offline
One problem is that people don’t communicate effectively. We see a lot of breakdown in communication within an organization because people become so dependent on email. If you see a suspicious wire transfer initiated by a fellow employee, take the time to walk to their desk and verify.
Beware the Internet of Things
With everything from refrigerators to thermostats now web-enabled, a small level of convenience can lead to massive vulnerability. Web-enabled appliances are easily accessible to hackers. However, companies continue to put IoT machines on secure networks. Take precautions on what devices you enable and how you do it.
Secure ironclad data backup protection
Reliable and regularly monitored data backups are the only way to recover after a malicious data breach. Despite this fact, a report by Storage Magazine found that one in three companies do not test their backups. At Capital Network Solutions, we exclusively use Barracuda Backup products to protect your data on-premises and in the cloud.
Invest in cyber insurance
Protect your organization against claims arising from ransomware and phishing attacks, especially if your business maintains or processes personal data like social security numbers and dates of birth, or protected health information like medical record numbers. Small business owners may not believe that the data they store qualifies as “sensitive.” But regardless of size, most organizations store valuable information like email addresses, billing addresses and phone numbers.
What are some of the top cyber security awareness training vendors?
Security awareness training is one of the fastest-growing sectors in the world of IT, as more companies realize that standard security measures like spam filters, antivirus software and firewalls aren’t enough on their own anymore. Here are three of the top vendors in this rapidly expanding sphere:
Celebrity hacker Kevin Mitnick serves as the Chief Hacking Officer for this Clearwater, Florida-based company, which specializes in the field of security awareness training. The company’s slogan: “Human Error. Conquered.”
This British corporation first started offering antivirus and encryption products in 1985. Today, Sophos helps secure the networks of over 100,000 businesses, including Pixar, Xerox, Ford, Avis and Toshiba. Meanwhile, their security training awareness software is called Phish Threat.
Founded in 2003, Barracuda runs operations from its headquarters in Campbell, California. A long-time leader in the data backup protection field, Barracuda entered the security awareness training sphere with PhishLine.
What else do I need to protect my business against security threats?
At Capital Network Solutions, we do a lot more than just “manage” your IT services. We proactively combat the threats of today and continuously evolve to meet the threats of tomorrow. Our certified technicians can monitor and update your system’s firewall, antivirus software, Windows security patches, onsite and offsite data storage and backup protection to help keep the bad guys out.